Configure OpenStack¶
Overview¶
In the previous section, we installed OpenStack. We are now going to configure OpenStack with the intent of making it consumable by regular users. Configuration will be performed by both the admin user and a non-admin user.
Domains, projects, users, and roles are a vital part of OpenStack operations. For the non-admin case, we’ll create a single domain with a single project and single user.
The tasks on this page should be performed on the host where the Juju client is installed.
Install the OpenStack clients¶
You’ll need the OpenStack clients in order to manage your cloud from the command line. Install them now:
sudo snap install openstackclients
Create the admin user environment¶
To gain control of the cloud the Keystone administrator password and the root CA certificate are needed. This information can be most easily obtained by using a file that is created for this purpose - often called an “openrc” file.
Download the openrc file and store it in a safe place.
When you want to use this file, source it. Assuming it’s now in your home directory:
source ~/openrc
The admin user environment should now be set up. Verify this with the env command:
env | grep OS_
Sample output:
OS_AUTH_URL=https://10.246.114.72:5000/v3
OS_USERNAME=admin
OS_PASSWORD=miuPaisoe7nuth3b
OS_USER_DOMAIN_NAME=admin_domain
OS_PROJECT_NAME=admin
OS_PROJECT_DOMAIN_NAME=admin_domain
OS_AUTH_VERSION=3
OS_IDENTITY_API_VERSION=3
OS_REGION_NAME=RegionOne
OS_AUTH_PROTOCOL=https
OS_CACERT=/home/ubuntu/snap/openstackclients/common/root-ca.crt
OS_AUTH_TYPE=password
Perform actions as the admin user¶
The actions in this section should be performed as user ‘admin’.
Confirm the user environment¶
One way that you can confirm that the admin environment is set correctly is by querying for cloud endpoints:
openstack endpoint list --interface admin
The output will look similar to this:
+----------------------------------+-----------+--------------+--------------+---------+-----------+---------------------------------------------+
| ID | Region | Service Name | Service Type | Enabled | Interface | URL |
+----------------------------------+-----------+--------------+--------------+---------+-----------+---------------------------------------------+
| 0d6fd05701f843e3b52e541bc346bbb7 | RegionOne | neutron | network | True | admin | https://10.246.114.71:9696 |
| 2e81734cf49e4ab2bfd46ae6ec53a45c | RegionOne | placement | placement | True | admin | https://10.246.114.75:8778 |
| 6391cb50e823478f952cecbb86c7b77e | RegionOne | glance | image | True | admin | https://10.246.114.77:9292 |
| 6ccfa872775d49ceab6fdc532b3366b2 | RegionOne | keystone | identity | True | admin | https://10.246.114.72:35357/v3 |
| 9d2bf9caf3eb40599be7ab482d118de3 | RegionOne | nova | compute | True | admin | https://10.246.114.74:8774/v2.1 |
| e4abf3a678a74cb994c0f77bc14d290a | RegionOne | cinderv3 | volumev3 | True | admin | https://10.246.114.81:8776/v3/$(tenant_id)s |
+----------------------------------+-----------+--------------+--------------+---------+-----------+---------------------------------------------+
If the endpoints aren’t displayed, it’s likely your environment variables aren’t set correctly.
Note
The helper files will set the Keystone endpoint variable OS_AUTH_URL to
use HTTPS if TLS is detected anywhere in the cloud. This will always be the
case due to the OVN requirement for TLS. If Keystone is not TLS-enabled (for
some reason) you will need to manually reset the above variable to use HTTP.
Create an image and flavor¶
Import a boot image into Glance to create server instances with. Here we import a Jammy amd64 image:
mkdir ~/cloud-images
wget http://cloud-images.ubuntu.com/jammy/current/jammy-server-cloudimg-amd64.img \
-O ~/cloud-images/jammy-amd64.img
Now import the image and call it ‘jammy-amd64’:
openstack image create --public --container-format bare \
--disk-format qcow2 --file ~/cloud-images/jammy-amd64.img \
jammy-amd64
Create at least one flavor to define a hardware profile for new instances. Here we create one called ‘m1.small’:
openstack flavor create --ram 2048 --disk 20 --ephemeral 20 m1.small
Make sure that your MAAS nodes can accommodate the flavor’s resources.
Set up public networking¶
Create an external public (shared) network, here called ‘ext_net’. We use the ‘flat’ network provider type and its provider ‘physnet1’ that were set up during the Neutron networking step on the previous page:
openstack network create --external --share \
--provider-network-type flat --provider-physical-network physnet1 \
ext_net
Create the subnet, here called ‘ext_subnet’, for the above network. The values used are based on the local environment. For instance, recall that our MAAS subnet is ‘10.246.112.0/21’:
openstack subnet create --network ext_net --no-dhcp \
--gateway 10.246.112.1 --subnet-range 10.246.112.0/21 \
--allocation-pool start=10.246.116.23,end=10.246.116.87 \
ext_subnet
Important
The addresses in the public subnet allocation pool are managed within OpenStack but they also reside on the subnet managed by MAAS. It is important to tell MAAS to never use this address range. This is done via a Reserved IP range in MAAS.
Create the non-admin user environment¶
Create a new domain, project, and user. Here we’ll use ‘domain1’, ‘project1’, and ‘user1’ respectively. You will be prompted to provide the new user’s password:
openstack domain create domain1
openstack project create --domain domain1 project1
openstack user create --domain domain1 --project project1 --password-prompt user1
Sample output from the last command:
User Password:********
Repeat User Password:********
+---------------------+----------------------------------+
| Field | Value |
+---------------------+----------------------------------+
| default_project_id | a67881c23bc840928b89054f35a6210e |
| domain_id | 228443ef0e054a89a36d75261b6531e9 |
| enabled | True |
| id | 37a3ab572ea14e659f1d885d44147b8a |
| name | user1 |
| options | {} |
| password_expires_at | None |
+---------------------+----------------------------------+
We’ll use the user’s ID to assign her the ‘Member’ role:
openstack role add --user 37a3ab572ea14e659f1d885d44147b8a \
--project project1 Member
Create an OpenStack user authentication file for user ‘user1’. All we’re missing is the Keystone URL, which we can get from the current user ‘admin’ environment:
echo $OS_AUTH_URL
The output for the last command for this example is https://10.246.114.72:5000/v3.
The contents of the file, say project1-rc, will therefore look like this
(assuming the user password is ‘ubuntu’):
export OS_AUTH_URL=https://10.246.114.72:5000/v3
export OS_USERNAME=user1
export OS_PASSWORD=ubuntu
export OS_USER_DOMAIN_NAME=domain1
export OS_PROJECT_NAME=project1
export OS_PROJECT_DOMAIN_NAME=domain1
export OS_AUTH_VERSION=3
export OS_IDENTITY_API_VERSION=3
export OS_REGION_NAME=RegionOne
export OS_AUTH_PROTOCOL=https
export OS_CACERT=/home/ubuntu/snap/openstackclients/common/root-ca.crt
export OS_AUTH_TYPE=password
Source the file to become the non-admin user:
source project1-rc
echo $OS_USERNAME
The output for the last command should be user1.
Perform actions as the non-admin user¶
The actions in this section should be performed as user ‘user1’.
Set the user environment¶
Perform a cloud query to ensure the user environment is functioning correctly:
openstack image list
+--------------------------------------+-------------+--------+
| ID | Name | Status |
+--------------------------------------+-------------+--------+
| 82517c74-1226-4dab-8a6b-59b4fe07f681 | jammy-amd64 | active |
+--------------------------------------+-------------+--------+
The image that was previously imported by the admin user should be returned.
Set up private networking¶
In order to get a fixed IP address to access any created instances we need a project-specific network with a private subnet. We’ll also need a router to link this network to the public network created earlier.
The non-admin user now creates a private internal network called ‘user1_net’ and an accompanying subnet called ‘user1_subnet’ (here the DNS server is the MAAS server at 10.246.112.3, but adjust to local conditions):
openstack network create --internal user1_net
openstack subnet create --network user1_net --dns-nameserver 10.246.112.3 \
--subnet-range 192.168.0/24 \
--allocation-pool start=192.168.0.10,end=192.168.0.99 \
user1_subnet
Now a router called ‘user1_router’ is created, added to the subnet, and told to use the public external network as its gateway network:
openstack router create user1_router
openstack router add subnet user1_router user1_subnet
openstack router set user1_router --external-gateway ext_net
Configure SSH and security groups¶
An SSH keypair needs to be imported into the cloud in order to access your instances.
Generate one first if you do not yet have one. This command creates a
passphraseless keypair (remove the -N option to avoid that):
mkdir ~/cloud-keys
ssh-keygen -q -N '' -f ~/cloud-keys/user1-key
To import a keypair:
openstack keypair create --public-key ~/cloud-keys/user1-key.pub user1
Security groups will need to be configured to allow the passing of SSH traffic. You can alter the default group rules or create a new group with its own rules. We do the latter by creating a group called ‘Allow_SSH’:
openstack security group create --description 'Allow SSH' Allow_SSH
openstack security group rule create --proto tcp --dst-port 22 Allow_SSH
Create and access an instance¶
Create a Jammy amd64 instance called ‘jammy-1’:
openstack server create --image jammy-amd64 --flavor m1.small \
--key-name user1 --network user1_net --security-group Allow_SSH \
jammy-1
Request and assign a floating IP address to the new instance:
FLOATING_IP=$(openstack floating ip create -f value -c floating_ip_address ext_net)
openstack server add floating ip jammy-1 $FLOATING_IP
Ask for a listing of all instances within the context of the current project (‘project1’):
openstack server list
Sample output:
+--------------------------------------+---------+--------+---------------------------------------+-------------+----------+
| ID | Name | Status | Networks | Image | Flavor |
+--------------------------------------+---------+--------+---------------------------------------+-------------+----------+
| 627a33c8-3c55-4878-bce3-3c12fc04e4b9 | jammy-1 | ACTIVE | user1_net=10.246.116.39, 192.168.0.98 | jammy-amd64 | m1.small |
+--------------------------------------+---------+--------+---------------------------------------+-------------+----------+
The first address listed is in the private network and the second one is in the public network:
You can monitor the booting of the instance with this command:
openstack console log show jammy-1
The instance is ready when the output contains:
.
.
.
Ubuntu 22.04.3 LTS jammy-1 ttyS0
jammy-1 login:
Connect to the instance in this way:
ssh -i ~/cloud-keys/user1-key ubuntu@$FLOATING_IP
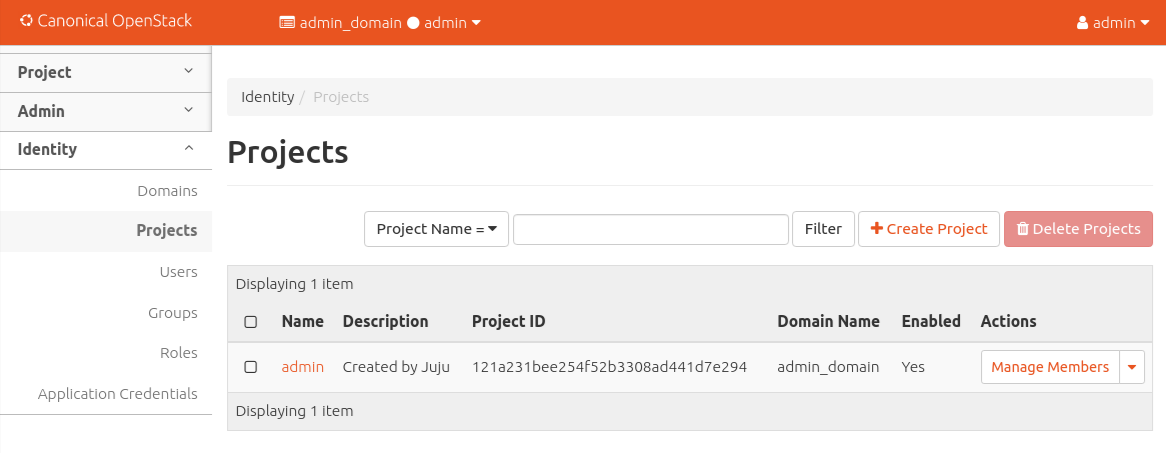
Dashboard access¶
To log in to the Horizon dashboard you will need its IP address and the admin password.
Obtain the address in this way:
juju status --format=yaml openstack-dashboard | grep public-address | awk '{print $2}' | head -1
In this example, the address is ‘10.246.114.76’.
The password can be queried from Keystone:
juju exec --unit keystone/leader leader-get admin_passwd
The dashboard URL then becomes:
http://10.246.114.76/horizon
The final credentials needed to log in are:
Once logged in you should see something like this:
VM consoles¶
Enable a remote access protocol such as novnc (or spice) if you want to connect to VM consoles from within the dashboard:
juju config nova-cloud-controller console-access-protocol=novnc
Next steps¶
You now have a functional OpenStack cloud managed by MAAS-backed Juju.
Important
Now that the cloud is deployed, the following management practices related to charm versions and machine series are recommended:
The entire suite of charms used to manage the cloud should be upgraded to the latest stable charm revision before any major change is made to the cloud (e.g. migrating to new charms, upgrading cloud services, upgrading machine series). See Charms upgrade in the Charm Guide for details.
The Juju machines that comprise the cloud should all be running the same series (e.g. ‘focal’ or ‘jammy’, but not a mix of the two). See Series upgrade in the Charm Guide for details.
As next steps, consider browsing these documentation sources:
OpenStack Charm Guide: the primary source of information for OpenStack charms
OpenStack Administrator Guides: upstream OpenStack administrative help
